Conflict today doesn’t just play out on land, sea, or in the air. It’s expanded into cyberspace.
Behind every headline of breaches and takedowns are targeted campaigns carried out by methodical, well-resourced threat actors — each with their motives, tactics, and long-term goals.
One such group is Salt Typhoon (also tracked as FamousSparrow and GhostEmperor depending on the vendor).
A Chinese nation-state–backed adversary that has been discovered infiltrating major U.S. telecom networks — from T-Mobile to Verizon, Samsung, and others.
Salt Typhoon is known for stealth, patience, and precision.
They leave behind only faint traces across compromised networks, making it exceptionally difficult for defenders to contain or eradicate their activity.
That challenge is exactly where cyber threat intelligence (CTI) comes in.
From IOCs to Insight
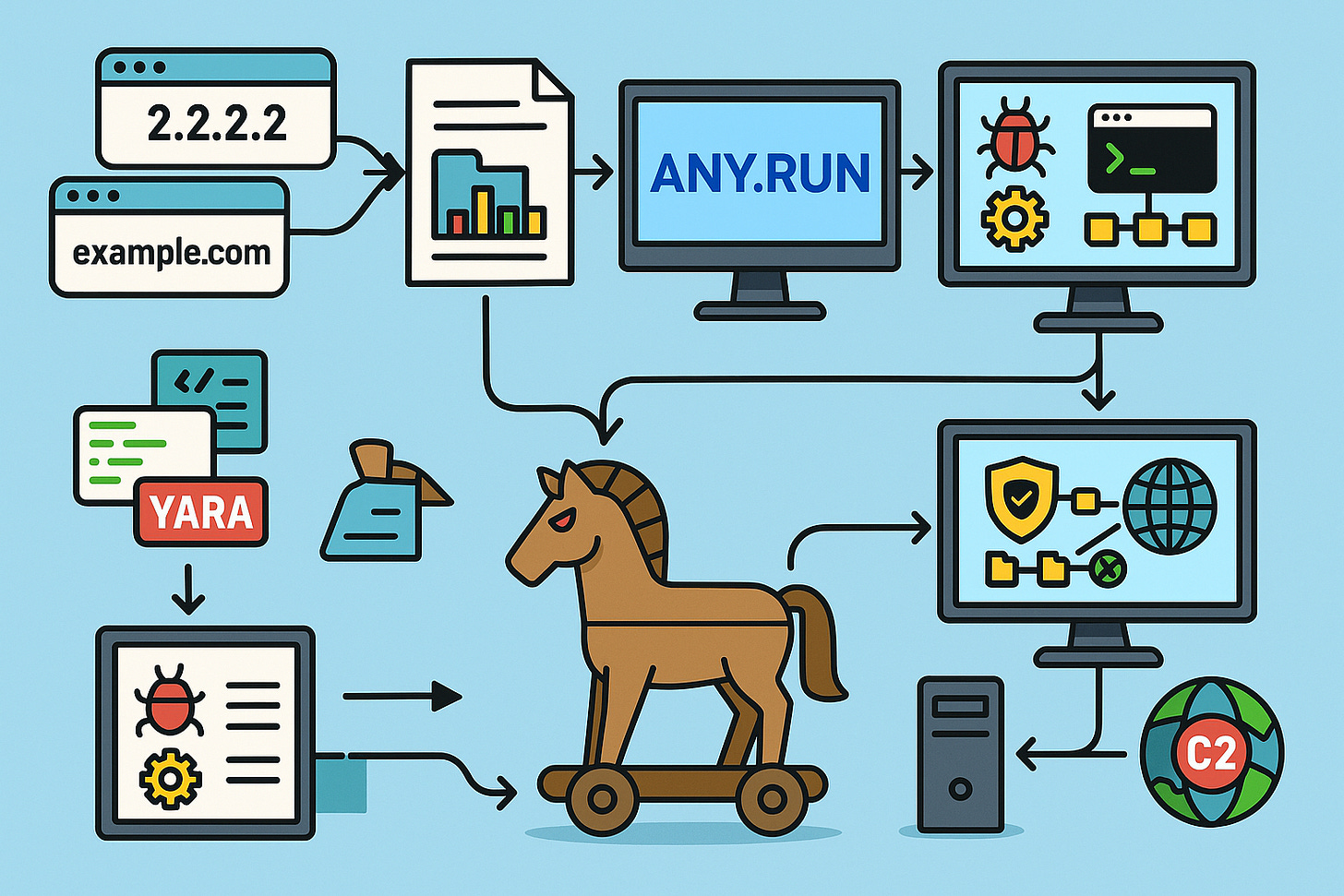
Threat intelligence is not just about collecting IOCs (indicators of compromise, such as hashes, IPs, and domains) and feeding them into SIEMs.
At its best, CTI is about connecting the dots: finding patterns across disparate indicators, uncovering infrastructure, profiling adversary behavior, and turning raw data into actionable defense.
The value lies in the transformation:
From a file hash → to the malware family behind it.
From a suspicious domain → to the broader C2 network.
From isolated alerts → to an adversary campaign strategy.
When done well, this enables defenders to build more effective detections, strengthen playbooks, automate enrichment, and prioritize risks in line with evolving active threat landscapes.
About Me
If you're new here, I'm Day, a Cybersecurity Engineer at Amazon. With five years in cybersecurity, my experience covers Detection Engineering, Cloud Security, Incident Response, Threat Hunting, and most recently, Threat Intelligence.
Before Amazon, I worked at Datadog as a cloud threat detection engineer, where I researched cloud threats and built detections for various cloud providers and SaaS applications.
I've worked my way up from various SOC analyst roles, investigating everything from endpoint threats to building detection systems for cloud-based abuse, so I know exactly what it takes to break into this field and make career advancements.
I started, just like many of you, learning from scratch, asking questions, and figuring it out one step at a time. And now, I'm here to help you do the same.
If you want to stay up-to-date on the cybersecurity industry and everything technical and career-related, be sure to like and subscribe to the newsletter for more content like this.
Join a vibrant cybersecurity community of over 6,500 people who are constantly engaging in conversations and supporting one another, covering topics from cybersecurity and college to certifications, resume assistance, and various non-professional interests like fitness, finance, anime, and other exciting subjects.
Applying CTI in Practice
As a Security Engineer at Amazon, I’ve had the opportunity to use threat intelligence at scale.
But CTI isn’t just for enterprise SOCs. With the right tools, individual analysts and researchers can explore and learn from the same adversary tradecraft.
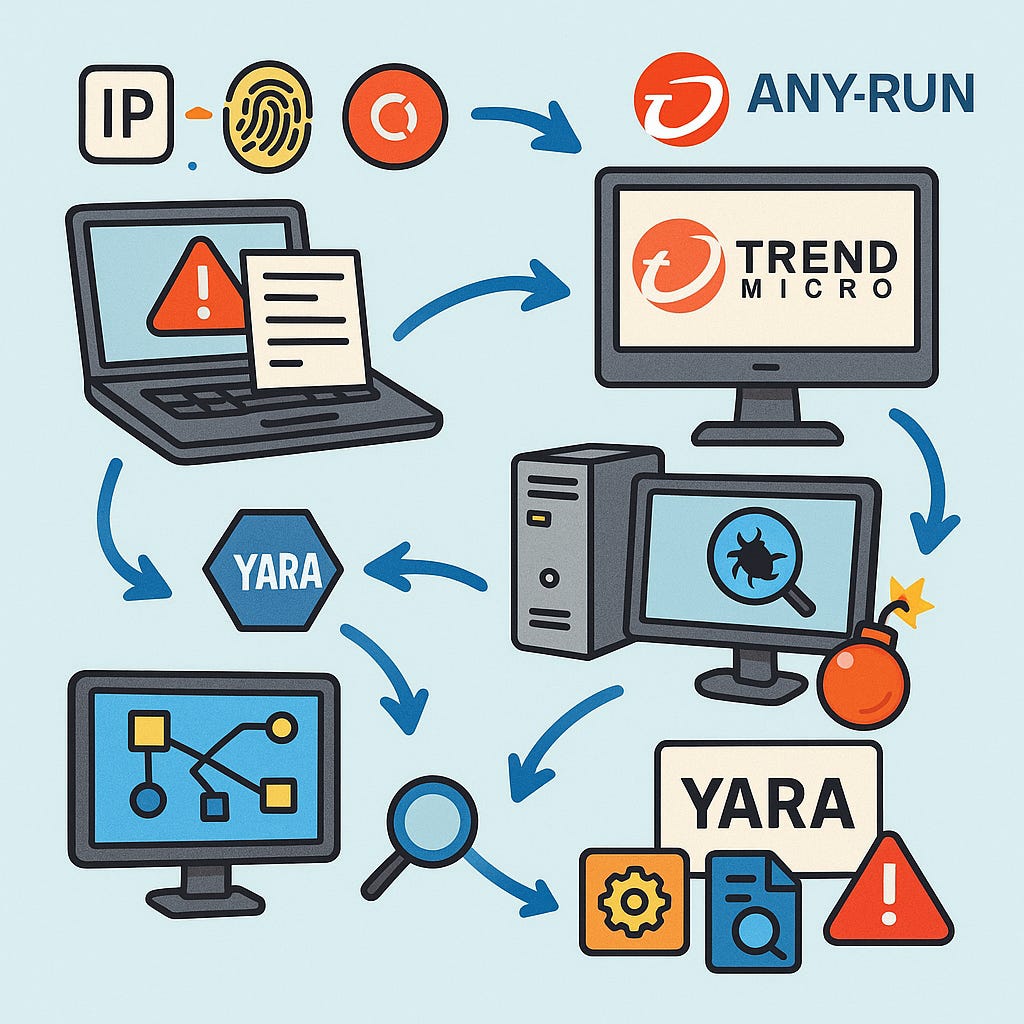
For this issue, I investigated Salt Typhoon using ANY.RUN’s Threat Intelligence Platform. It blends interactive sandboxing (their signature strength) with curated intelligence and lookup capabilities. Here’s what that looks like in practice:
Starting with a handful of IOCs, such as an IP address, a SHA-256 hash, or a domain name.
Pivoting into reports → correlating with published research from vendors like Trend Micro.
Interactive detonation → running suspicious files in a sandbox, observing process creation, persistence mechanisms, and outbound C2 calls.
Hunting for connections → mapping behaviors against known TTPs and extracting new indicators.
YARA integration → building and running rules directly in the platform to surface related artifacts.
What begins as a single suspicious hash quickly expands into a narrative: a Trojan is dropped, a service is created for persistence, reconnaissance of the host is conducted, and finally, communication with a C2 domain occurs.
Why It Matters
The power of CTI lies in turning fragments into a story.
Instead of drowning in endless IOCs, analysts can contextualize activity, link it to known actors, and anticipate what might come next.
In this case, a few scattered data points around Salt Typhoon transformed into a clearer picture of:
Their infrastructure choices
Their persistence techniques
Their reconnaissance behavior
Their communication patterns
With that knowledge, defenders can proactively hunt for related TTPs in their environments or simulate adversary behavior to test defenses.
ANY.RUN Threat Intelligence
This issue is powered by ANY.RUN, which sponsored this deep dive. ANY.RUN makes it easy to turn raw indicators into actionable intelligence without needing to set up your own lab environment. If you’re serious about developing threat intelligence skills, it’s worth checking out.
Closing
What began as a file hash and a suspicious domain evolved into a broader narrative about Salt Typhoon’s operations. That’s the heart of cyber threat intelligence: transforming raw signals into stories that defenders can act on.
If you’re early in your cybersecurity journey, practice this workflow yourself:
Begin with a known IOC from a publicly available report.
Pivot into related domains, files, and hashes.
Map the TTPs you discover against frameworks like MITRE ATT&CK.
Build detections or run hunts based on your findings.
That’s how you transition from merely “consuming” intel to generating actionable intelligence — a skill that grows from home labs to Fortune 500 SOCs.
Here’s a video that can help you do that:
Thanks for reading Cyberwox Unplugged! This post is public, so feel free to share it.